As organizations rapidly adopt AI agents for autonomous workflows, traditional identity and access management (IAM) systems—built for deterministic users and predictable processes—are no longer sufficient. AI agents introduce non-deterministic behaviors, delegation chains, and ephemeral needs that demand a fundamentally new authorization model. HashiCorp Vault is rising to the challenge with a set of native features designed specifically for these autonomous actors. Here are the five critical capabilities you need to understand about Vault's new AI agent support.
1. The Shift from Deterministic to Non-Deterministic Authorization
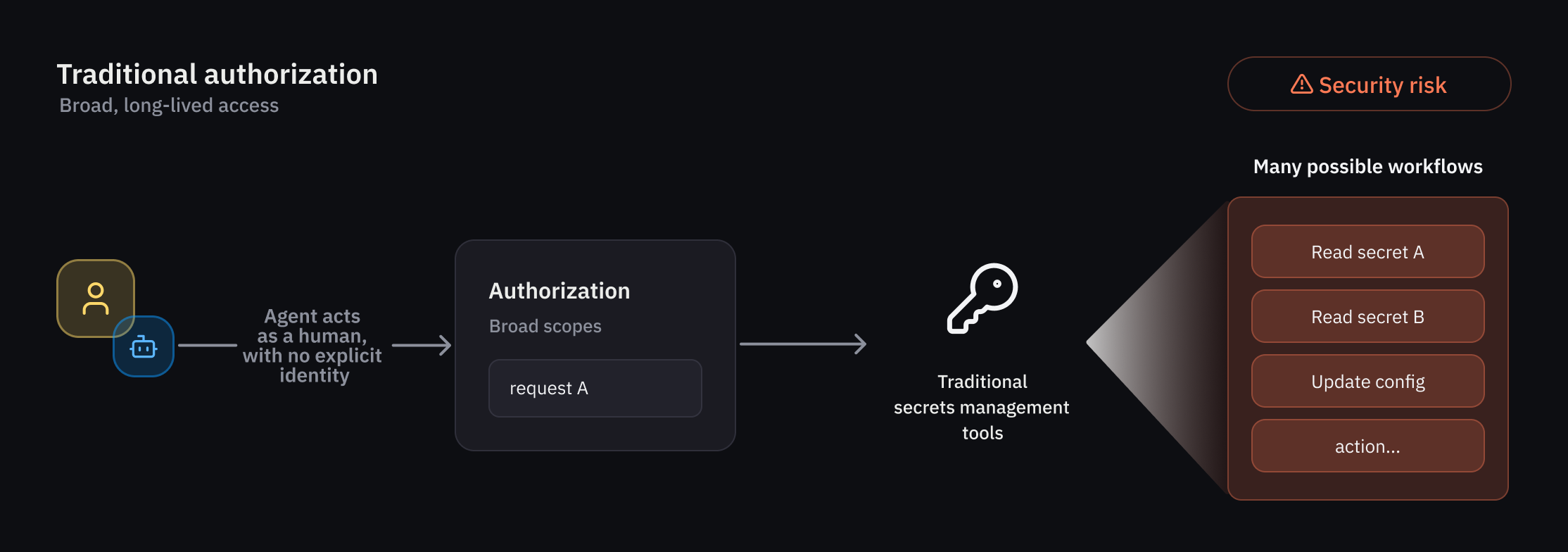
Traditional IAM assumes users follow predefined steps and workflows. AI agents, in contrast, operate autonomously and can take unpredictable paths to achieve goals. This requires an authorization model that combines identity with runtime policy evaluation and ephemeral permissions. Vault now evaluates authorization at the moment of each request, granting temporary, tightly scoped access that expires immediately after the task completes. This shift reduces the risk of standing privileges and ensures that agents can only act within the guardrails set by administrators, even when their exact actions are unknown in advance.
2. Introducing the Agent Registry – A Dedicated Identity Primitive
To manage agent identities separately from humans and traditional non-human identities (NHIs), Vault introduces the agent registry. This new primitive allows developers to register and track agent activity in a dedicated system. Once registered, each agent receives a unique identity that is used for all subsequent authorization decisions. The registry is particularly crucial for delegation flows, where an agent acts on behalf of a human using an on-behalf-of (OBO) pattern. By explicitly tracking these delegations with consent, the agent registry provides a clear audit trail and forms the foundation for registration, authorization, credential management, and observability of all agent actions.
3. Granular Identity-Based Policies for Agents
Least privilege access is paramount when dealing with unpredictable agents. Vault enforces this through rich, granular identity-based policies that operate at runtime. Administrators can define deterministic guardrails—such as allowed actions, target systems, and time windows—that constrain an agent's behavior even when its path is non-deterministic. For example, a policy might allow an agent to read secrets only from a specific vault path and only between 9 AM and 5 PM. These policies are evaluated per request, ensuring that each action is authorized in the context of the agent's identity, its delegated authority, and the current transaction.
4. Ephemeral Authorization – Temporary, Scoped Access
AI agents often need access to secrets, credentials, or APIs for short-lived tasks. Vault's new ephemeral authorization controls provide exactly that: temporary access rights that expire after a specific action, workflow, or time period. Instead of issuing long-lived tokens, Vault generates time-bound credentials scoped to the agent's current request. This dramatically reduces the blast radius if an agent is compromised or behaves maliciously. The per-request authorization model ensures that even if an agent tries to reuse a credential, it will be denied because the token has already expired or the context has changed.
5. Delegation and Consent – On-Behalf-Of Patterns
One of the most powerful—and risky—capabilities of AI agents is the ability to act on behalf of a human user. Vault handles this with an explicit delegation and consent mechanism. When an agent uses an on-behalf-of (OBO) pattern, Vault verifies that the human user has granted consent for that specific agent and scope. All actions are audited with clear attribution, tying each agent action back to the delegating user. This standardized approach provides the visibility and control needed to safely enable agentic workflows across environments, without sacrificing security or compliance.
Conclusion
These five capabilities represent a major leap forward in securing AI agents at scale. HashiCorp Vault is currently offering these features through an early access program for select customers, with a broader public beta planned for this summer. By combining an agent registry, granular policies, ephemeral authorization, and delegation controls, Vault provides a standardized, identity-first framework that can adapt to the unique challenges of agentic AI. Organizations that adopt these tools now will be well-positioned to harness the power of autonomous agents without compromising on security.